It seems like we can’t go a week without hearing about a data breach or a situation in which personal data has been compromised. Unfortunately, cybercriminals are becoming more sophisticated in their antics and there is very little we can do to stop cyber attacks from happening.
We can, however, arm ourselves against hackers and identity thieves by first understanding the main ways in which our personal data can be compromised. Then, we can take necessary steps to safeguard our personal data and prevent criminals from accessing our private information.
Understanding How our Personal Data Gets Compromised
The fact of the matter is that there are many ways in which our personal data can become compromised. Yet, they all seem to boil down to five main reasons, some of which are under our control and some are not.
The Top 5 Ways Personal Data is Compromised:

1. Organizational Data Breach: In order to do business with us, organizations often require our personal information. From financial institutions and credit bureaus to medical groups, email and social media platforms, subscription-based platforms and data-storage cloud companies…the list goes on. We trust that the organization follows its outlined security protocols to keep our private information, private. When that organization fails to deliver on its security measures, as we’ve collectively witnessed with the recent onslaught of big-data and cloud-system security breaches, our personal information is subject to unauthorized access and theft. Be sure you trust the organization and understand its data management policies and procedures for how your personal data will be used, stored, secured and destroyed before sharing personal information.
2. Unsecured Internet Connection: Even though it’s enticing to stop in to your local coffee shop or public library to work remotely from your laptop or portable device, you should always check the security of the internet connection you’re about to use, first. Public or otherwise unsecured connections are the most susceptible to cyber-criminal activity; using an unsecured internet connection is like inviting the hackers to your doorstep. In short, if the internet connection can be accessed without a password, don’t connect to it.
3. Unsecured Device: The same can be said for any device you use to access the internet. From smartphones to laptops and tablets and now smart home devices like Amazon Echo and Google Home; these devices hold troves of our personal and private data. Maintaining updated security software, firewalls and installing extra security like a two-way authenticator are imperative to ensuring your device is protected from outside penetration. Password strength also falls under device security. Passwords should never be the same, should include characters and numbers as well as letters and should never be something easily guessed about yourself. Even if you are using a secured internet connection, the lack of security or lack of updated security for your device is just another invitation for having your data stolen.
4. Responding to a Scam: Scams are designed to look, read and feel as authentic a communication as possible. Email phishing, ‘robo’ calls and social engineering tactics like personality quizzes are just a few examples of the ever-growing scams hackers and cyber criminals have developed to steal your personal data—right from the horse’s mouth. We often (mistakenly) place our trust blindly into communication efforts like email, phone and social media because those are places we communicate with people and brands we do trust. Always be vigilant of the type of organization and the way in which they communicate with you before you answer. (The IRS, for instance, will never email you or call you for personal information.)
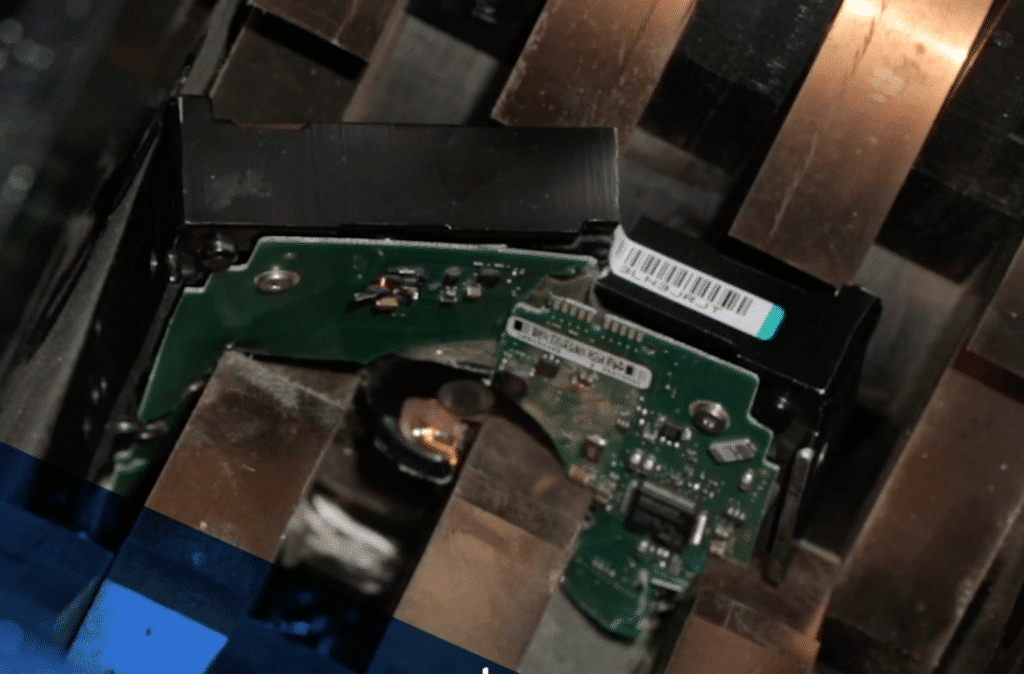
5. Data Storage and Disposal at Home: Probably one of the most overlooked ways in which our personal data can be compromised is how we manage our data at home. Do you have a safe, secure, and designated location at home for all your personal and private documents? (You should.) And, what do you do with sensitive information that you no longer need, like an expired credit card or an old bank statement? If your answer is to cut it up and throw it out, you’re putting your personal data at risk. This also holds true of old devices you want to get rid of. Consider the personal information amassed on the hard drives of your old laptop, tablet, smartphone or other data-storing device. If you don’t properly destroy the hard drive, the data can still be reconstructed and accessed long after you’ve disposed of the device (say, if you turned it over to a buy-back program or, worse, threw it in the trash for a dumpster-diver to find).
Proper Data Destruction and Disposal
While there’s little you can personally do to protect your information from a data breach at an organization, ensuring that the companies with whom you do business have a comprehensive data security and destruction policy is a good first step. There are also ways for you to better control your own data security. Taking steps like assessing your internet connections and device security and thinking before you respond to any digital or telephoned communication can greatly help you ensure your private data stays secure and remains uncompromised.
When it comes to home security measures and data disposal, we recommend you maintain a specific and private place for anything that contains your personal information, and that you bring end-of-life devices to a local data destruction day, often held at universities in the spring. Of course, if you are in the area, you are always welcome to bring your device to SEM for physical destruction. As a final note, if your personal data has been compromised and you’ve become a victim of identity theft, you should report the identity theft incident to the Federal Trade Commission (FTC) online at IdentityTheft.gov or by phone at 1-877-438-4338.